Zero Trust Architecture (ZTA) and Blockchain are the two concepts that are making a buzz in the cryptosecurity world. In this blog, you will understand the concept of zero-trust architecture and blockchain, how they work, and how they can be used to increase security.
What is Zero Trust Architecture (ZTA)?
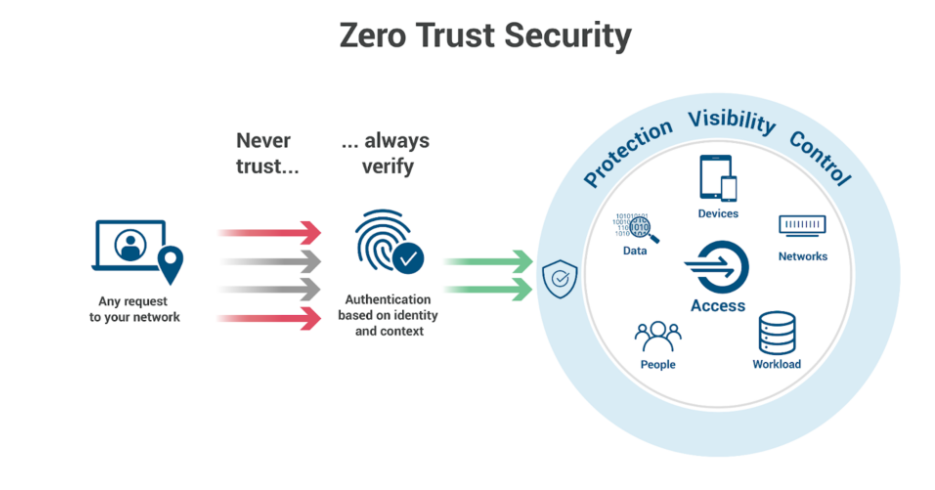
Never trust, always verify is the principle of Zero Trust Architecture. It is a security model. Zero Trust architecture needs continuous verification of all entities trying to access it; it’s not like traditional security models that assume everything within the network is trustworthy. Zero recognizes that threats can be internal or external.
Core Principles of Zero Trust
Each access on Zero Trust is verified and authorized. It is a continuous process and not a one-time thing. This increases the security of the network.
Users and systems have the minimum resources to carry out their tasks. This reduces the risk of a potential attack.
To reduce threats, the network is divided into small segments.
Why is Zero Trust Important?
Traditional defense systems are no longer sufficient against modern cyber-attacks. Phishing attacks and advanced persistent threats (APTs) can easily bypass the conventional security system. To win against these threats, Zero Trust provides a more secure and flexible approach.
What is Blockchain?
A decentralized digital ledger that allows data to be recorded securely and transparently is known as a Blockchain. Popular currencies like Bitcoin and Ethereum use Blockchain technology.
How does it work?
Blockchain is Decentralized, which means it works independently and is not controlled by any authority. It uses a peer-to-peer network.
Participants can access each transaction, which is recorded on a public ledger. This ensures transparency in the network.
You cannot change or delete the data once added on Blockchain. This ensures data integrity.
Key Features of Blockchain
Users are provided with high security as all data is encrypted.
A proof of work (POW) or proof of stake (POS) mechanism is used to ensure all the nodes agree on the validity of transactions.
Smart contracts, whose terms are directly written in codes, are used to maintain automated transactions.
Integrating Zero Trust Architecture with Blockchain
Blockchain, combined with zero Trust, provides a formidable approach to security.
Blockchain ensures that data cannot be modified, and Zero Trust continuously verifies the access for this data. Hence, data is integrated and authenticated.
Zero Trust can securely verify Decentralized identities that Blockchains create.
Blockchain transactions are initiated by users who Zero Trust authorizes. This protects the Blockchains from unauthorized access.
Implementing Zero Trust in Blockchain Environments
Zero Trust principles help in monitoring every interaction within the Blockchains.
Users’ identities are verified before they interact with different Blockchain.
In Blockchain, each data is encrypted to protect it from unauthorized access.
Challenges and Solutions of Zero Trust Architecture & Blockchain
Zero Trust Architecture
Challenges:
Organizational culture requires a change, and working as Zero Trust is complex while executing.
Users’ experience can be affected by continuous verification if not applied carefully.
Solutions:
Automation tools reduce manual workload and errors for continuous, smooth verification.
Users must be educated and trained on security and how Zero Trust can protect them against potential theft.
Blockchain
Challenges:
Scalability is a significant issue in Blockchain, as the network can struggle due to the consensus mechanism
The proof of work (POW) mechanism can consume much energy and is environmentally unsupportive.
Solutions:
Scalability within Blockchain can be increased using Layer 2 solutions like sidechains and off-chain transactions.
Use mechanisms like Proof of Stake (PoS) or Delegated Proof of Stake (DPoS) as they are energy efficient.
Conclusion
Modern cybersecurity needs important components like Zero Trust and Blockchain. Organizations can increase their security by understanding and using these technologies.
To protect the system and data against threats, a powerful combination of Zero Trust and Blockchain is used as it ensures continuous verification and that data is stored securely.
Disclaimer
This article is for informational purposes only and provides no financial, investment, or other advice. The author or any people mentioned in this article are not responsible for any financial loss that may occur from investing in or trading. Please do your research before making any financial decisions.




















