- Forta networks aim to provide security to smart contracts against attacks and zero-day vulnerabilities.
- The network uses Fort Bots for this purpose.
The idea of a Web3 network that integrates the concepts of blockchains, cryptocurrencies, and decentralized protocols is becoming sunnier with the booming of NFT marketplaces and the launch of meta-based games. As the network grows, so does the associated economy which is estimated to be around $27.5 Billion. It is all set to reach $81.5 Billion by 2030, resulting from the increase in transaction volume and total value locked.
However, there has also been an increase in hacks and exploits which amounted to $4 Billion in the year 2022. Developers perform several audits and security checks before finally releasing their platforms, but they have come out to be inefficient. Their delayed and slow response to attacks and zero-day exploits have led to the further increase in losses.
Some existing centralized financial service providers rely on services from third parties for their security from attacks, malware, and threats. They rely on antivirus scanners (Trend Micro, Kaspersky, etc), network log and traffic scanners (IBM, AWS Splunk, etc), and homegrown security scanners (Apache Kafka). These solutions involve using detection bots and machine learning, to find problems in the source code, libraries, or binaries. These solutions, however, fail to address a public and permissionless network.
The Web3 economy relies on smart contracts, where the terms and conditions of a deal are stored through programming and making it immutable once executed. This is necessary to maintain a reliable relationship between the parties involved. However, smart contracts have a very complex design and because of the continuous development of smart contract programming languages, it becomes impossible to identify all the vulnerabilities and risks involved. These risks extend themselves to users who rely on them for exchanges, oracles, and smart wallets, pushing them into a zone of potential hacks too.
How Does Forta Network Work?
Forta network is designed to prevent hacks and risks by real-time monitoring with the help of threat detection bots and scan nodes supporting any EVM-compatible L1 or L2.
Forta Node Software
The software is run by node operators who act as threat scanners and information providers forming a decentralized network. These scan nodes are responsible for scanning block-by-block state changes in the network and transactions and executing Forta bots. The software is written in Golang language and can be run on any standard server. This software is distributed only through a license right now to protect it from forked competitors and free-riders but soon will become an open source.
Forta Bots
These bots are created by security researchers and developers of the Forta community who stake their FORT tokens to prove themselves honest. These bots are responsible for checking individual transactions and the changing state of smart contracts to identify attacks or vulnerabilities. They utilize time series or machine-learning techniques for bug detection. After detecting a potential threat, it broadcasts an alert in the Forta network which is looked upon and resolved by the scan nodes.
Some bots are general and others are developed for specific smart contracts with in-built logic. In the future, more advanced bots will be created as more challenging threats are identified in complex smart contracts by the Forta community. These logics can be defined in any language like JavaScript, Go, Python, or Rust which is Docker-compatible. The Docker containers are used to deploy Forta bots which are registered by their creators through Forta smart contracts.
These bots can be used to identify issues like unusual transactions (flash loans and huge gas fees), abnormal withdrawals, rapid changes in liquidations and collateralization, and transactions that specifically target some identified loopholes.
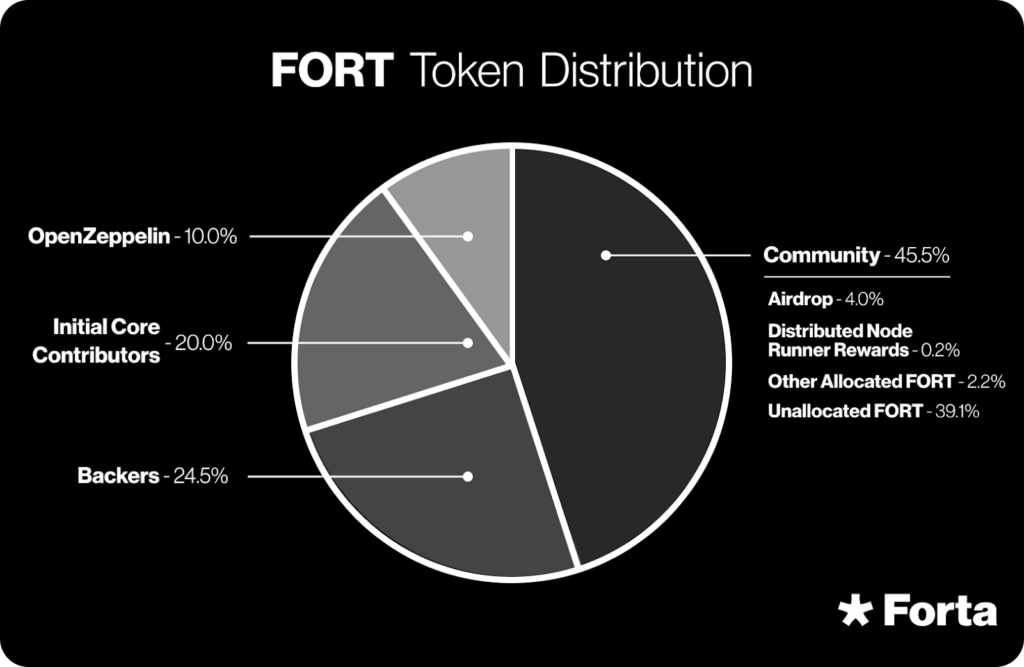
Forta Token
This token is an ERC-20 token, native to the network which is used for governance, staking, and slashing. Scan nodes need to stake a dedicated amount of FORT tokens to participate in the network activities and any suspicious action could lead to losing these tokens.
Final Thoughts
Some exploits like phishing, multi-chain or bridge attacks, and governance attacks can be identified in early stages and prevent large-scale fund losses. The Forta community has been successful in launching Microsoft ice phishing bots and Sleep Minting bots which can be used to detect such exploits. As the community expands, more researchers, developers, and security experts will join and develop techniques to prevent future attacks and zero-scale vulnerabilities.





















